Scammers Love the Moment Right After You Start Doubting
🔒 Leader's Dispatch: Volume 36 (Click to Catastrophe, Part 7 of 7 Part Series)
Episode 06: The Shutdown Playbook
Research Binder: the receipts (citations + source notes) are compiled in a PDF at the bottom of this article.
Fewer Clicks. Fewer Results.
👋 Welcome to my paid subscriber-only edition of Empathy Engine (🔒 Leader’s Dispatch). Each week I build evidence-forward tools for product leads who need to say no, defend tradeoffs, and lock in decisions before they get rewritten later.
“I think I may have moved too fast.”
That sentence rarely arrives at the beginning of a scam. It arrives after the switch. After the pressure. After the small compromises that sound responsible in the moment and reckless five minutes later.
Most teams think the scam wins at the moment of deception. That is the comforting version. The harder version: the real damage often begins after suspicion appears. When nobody owns the next move, everyone improvises in parallel, and the intervention window is already closing.
This final episode is about that window. Not one more script. Not one more “spot the red flag” exercise that leaves people stranded the moment the problem gets expensive.
This episode has one job: stop improvisation in the first hour.
TL;DR: Most teams improvise once suspicion appears and lose the intervention window. This is the 7-step first-hour protocol that stops the cascade.
Episode Promise
This is written for finance, operations, and customer-facing leaders. The people who have to decide what happens in the first 60 minutes. Use it as the playbook you reach for the moment someone says, “I think I may have moved too fast.”
Click-to-Catastrophe has spent this series mapping different storefronts for the same underlying machine. Pig butchering. SIM swap. Wire and invoice fraud. Refund and over-payment. Account takeover and fake support. Scam supply chain. Different costumes. Different entry points. Same pressure pattern once the system starts moving.
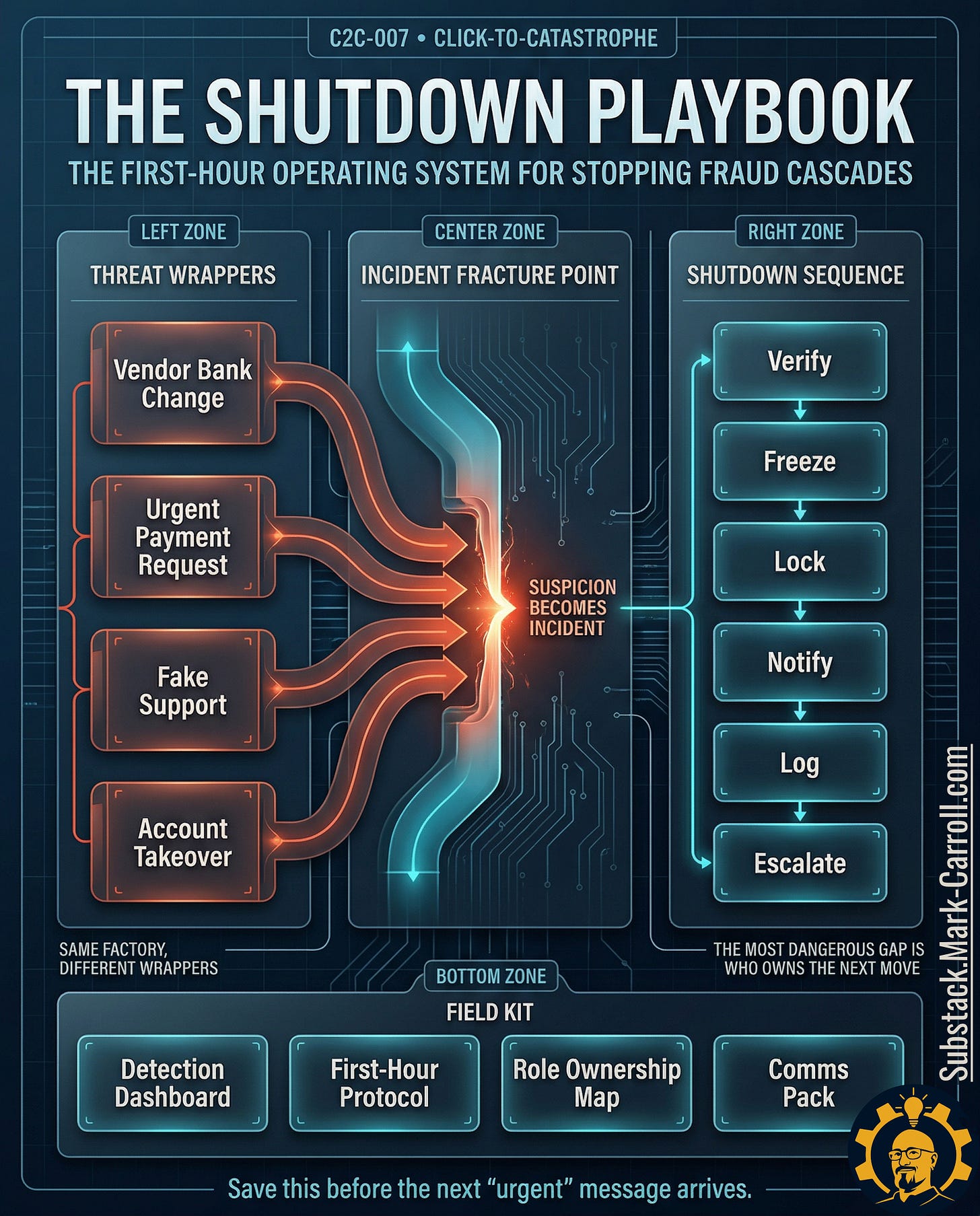
By the end of this piece, you will have four things: a universal detection dashboard, a cross-scam pattern map, a first-hour ownership and response protocol, and a communications pack that finance, operations, and customer-facing leaders can use before confusion becomes silence.
This is not scam trivia. This is the operating manual for the moment suspicion becomes incident.
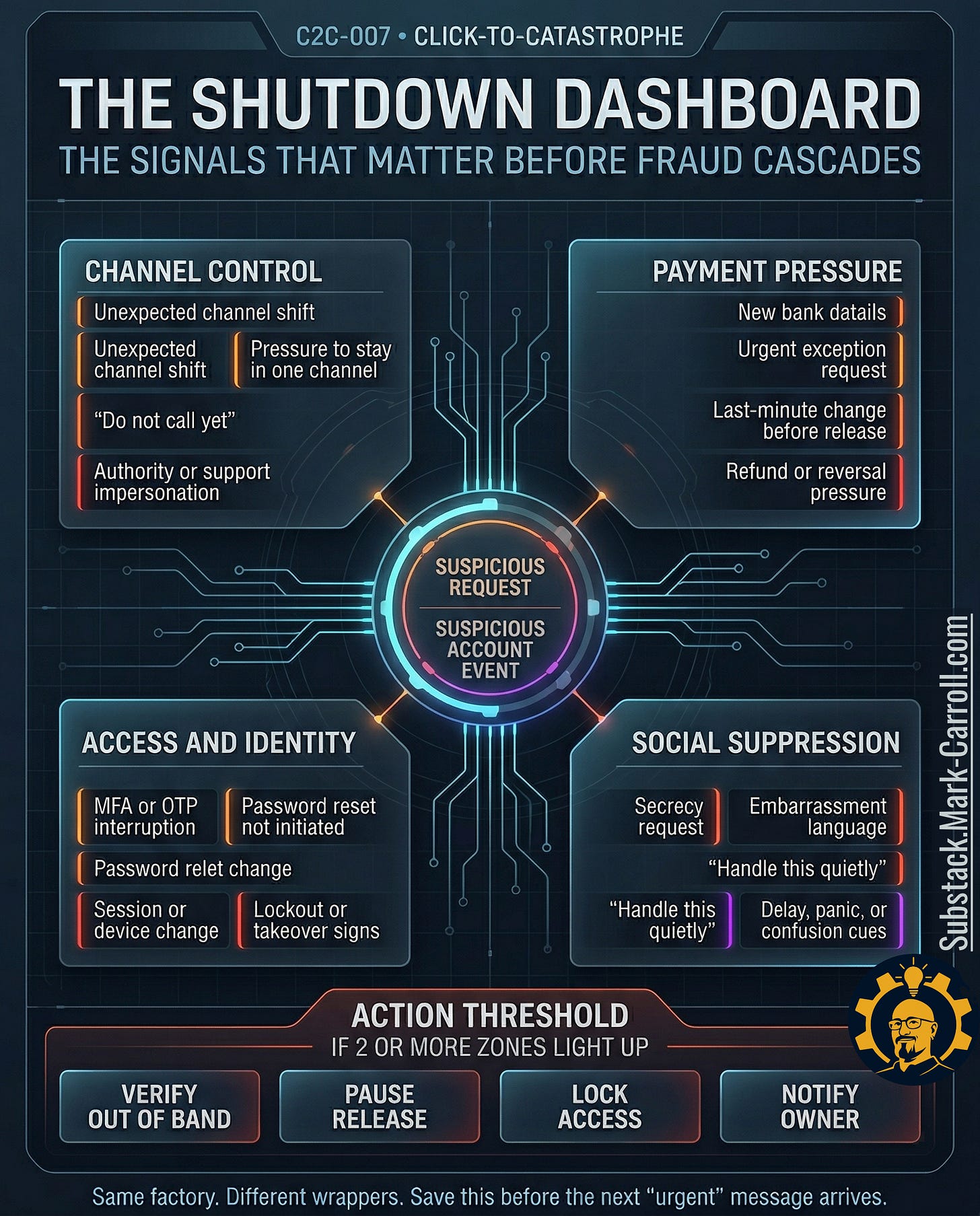
The Shutdown Dashboard
Most people start in the wrong place. They ask, “What kind of scam is this?” That question matters eventually. It does not matter first. The faster question: which signal zones are lighting up right now?
Zone 1: Channel Control. A request jumps channels. A caller tells you not to hang up. A vendor suddenly wants to stay inside email. A support voice says a callback will only slow the fix. The goal is not convenience. The goal is isolation.
Zone 2: Payment Pressure. New bank details. Same-day exception requests. A last-minute change right before release. A refund demand that turns urgency into obedience. Money movement only needs enough pressure to get around your pause button.
Zone 3: Access & Identity. A reset you did not initiate. MFA or OTP weirdness. A session that looks active when it should not. An account that locks you out while someone else glides through the front door.
Zone 4: Social Suppression. “Handle this quietly.” “Do not overreact.” “I am probably wrong.” Embarrassment language. Delay language. The phrases that turn a reportable incident into a private wrestling match.
Trigger rule: If two or more signal zones activate at once, stop interpreting and start the shutdown protocol.
Example: New bank details + “handle this quietly” = two zones = immediate pause, not discussion.
From that moment, the sequence is fixed: verify through the official out-of-band channel, pause any release, lock access, notify the named owner.
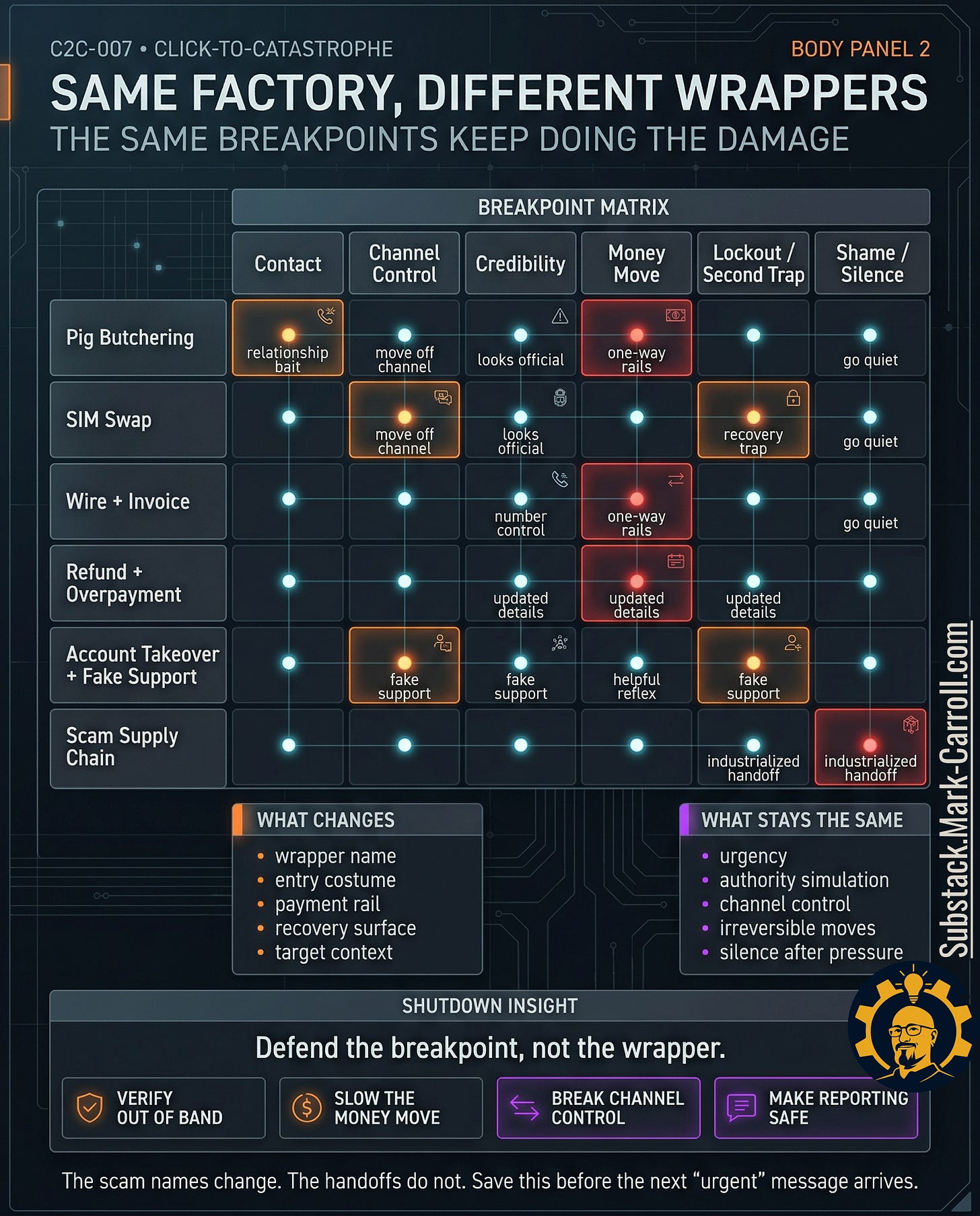
Same Factory, Different Wrappers
This series looks broad only if you read it at the wrapper level. At the breakpoint level, it has been telling one story the whole time.
Pig butchering opens with contact capture, grows through channel control, manufactures credibility, moves money, then leans on shame and silence to keep the victim alone.
SIM swap looks more technical, yet the pattern rhymes. Channel control shifts to the number. Credibility flows through systems that still treat the phone as proof. Lockout follows. Silence follows faster.
Wire and invoice fraud looks clean and professional. That is part of the trick. The channel stays familiar. The credibility is borrowed from real workflow. The money moves on a rail built for speed.
Refund and overpayment weaponizes helpfulness. Fake-clearing confusion softens the target. Urgency does the routing. The second trap appears when the victim tries to fix the mess quickly and cleanly.
Account takeover and fake support turns relief into the costume. Help sounds safe. Cooperation sounds careful. Then the code becomes the key, and the victim discovers that “password changed” and “attacker removed” are not the same event.
The scam supply chain made the ugliest point of the series plain. These are not isolated accidents. Tooling, scripts, marketplaces, and handoffs let attackers industrialize pressure. The storefront changes. The factory does not.
Defend the breakpoint, not the wrapper.
The breakpoints every scam moves through:
• Contact capture
• Channel control
• Credibility manufacture
• Lockout or second trap
• Shame and silence
The wrapper changes. The workflow does not.