$16.6B Lost. 859K+ Complaints. What to Do in 1 Hour?
🔒 Leader's Dispatch: Volume 32 (Click to Catastrophe, Part 3 of 7 Part Series)
Previous:
Episode 03: Wire and Invoice Fraud
Cold Open
Friday. 4:55 PM.
Month-end is loud. The AP queue is blinking. Someone important wants this cleared today.
A vendor “resends” an invoice. Everything looks normal. Familiar logo. Familiar tone. Familiar amount.
One tiny detail is different.
Bank details, updated.
That small change is the entire attack. The email is real. The vendor is real. The invoice amount is real. Only the destination has been swapped, and the payment rail does not care. The rail was built for speed, not second chances.
By the time anyone notices, the money is already somewhere else.
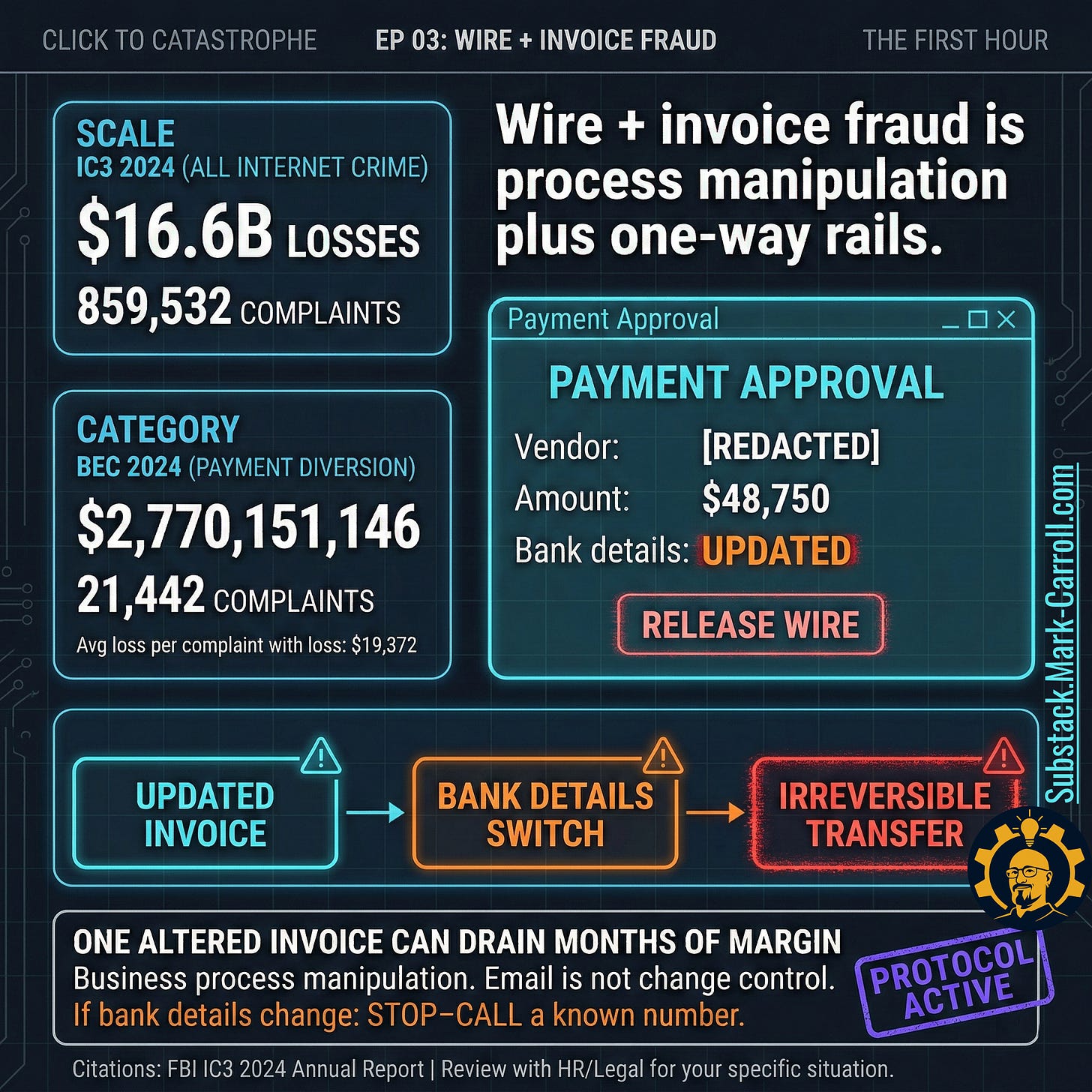
Scale check (so nobody hand-waves this away):
IC3 reported $16.6B in total internet-crime losses in 2024 across 859,532 complaints. (All citations are collected and organized at the bottom of this article in a research binder PDF.)
Business Email Compromise (BEC) shows $2,770,151,146 in losses in 2024 with 21,442 complaints.
Average reported loss per complaint with loss in 2024: $19,372.
Episode Promise
Episode 03 in Click to Catastrophe. Awareness training does not stop payment diversion. Operating gates do.
By the end, you will have:
A map of which payment rails do not rewind
A five-step STOP-CALL gate that breaks channel control
A maker-checker dual approval pattern that is not ceremonial
A vendor bank change tripwire that survives artificial urgency
Scripts that let a mid-level professional pause payment without getting crushed
A First 60 Minutes playbook that preserves your options when something slips
How It Works
Here is the insight that changes everything: fraud can succeed without fooling anyone. Speed does the work.
Most people picture fraud as a forgery, a fake invoice, a fake vendor, an email full of red flags. This version is different. The attacker does not fake the invoice. The attacker intercepts the process around it.
Picture a real scenario. Your company has worked with a supplier for two years. The relationship is normal. Invoices arrive regularly. One day, a message comes from that supplier’s email address, or one that looks like it, explaining they changed banks and asking you to update payment details before the next remittance. The message is polite. Professional. The amount matches what you expected.
Nothing is forged. Nothing looks wrong.
Only one element changes: the account number at the bottom. That number belongs to the attacker.
This is BEC in its most effective form: not deception through fabrication, deception through substitution. One false node inside an otherwise legitimate transaction. Your process does the rest.
The payment rail was designed for exactly this moment. Move money. Move it fast. No friction. No pause. No retrieval.
Speed is the weapon. Trust is the path. Channel control is how they keep you from asking the one question that collapses the entire attack.
Did you actually change your banking details?
A thirty-second call can collapse a billion-dollar class of fraud. The attacker’s strategy depends on you not making that call.
How It Spreads
It spreads through ordinary phrases:
“Resending invoice”
“We changed banks”
“Can you do a same-day wire”
“Don’t call, I’m traveling”
“Use this number”
Each phrase exists for one purpose: keep you in the channel.
The scam works because urgency becomes a permission slip. Under pressure, people override warnings, batch-approve queues, and rely on “someone else probably verified this.” Month-end pressure accelerates it. A fragile vendor relationship accelerates it. A tired AP professional who does not want a confrontation accelerates it.
Reminders are not controls. A reminder is hope with nicer typography.
Gates are controls.
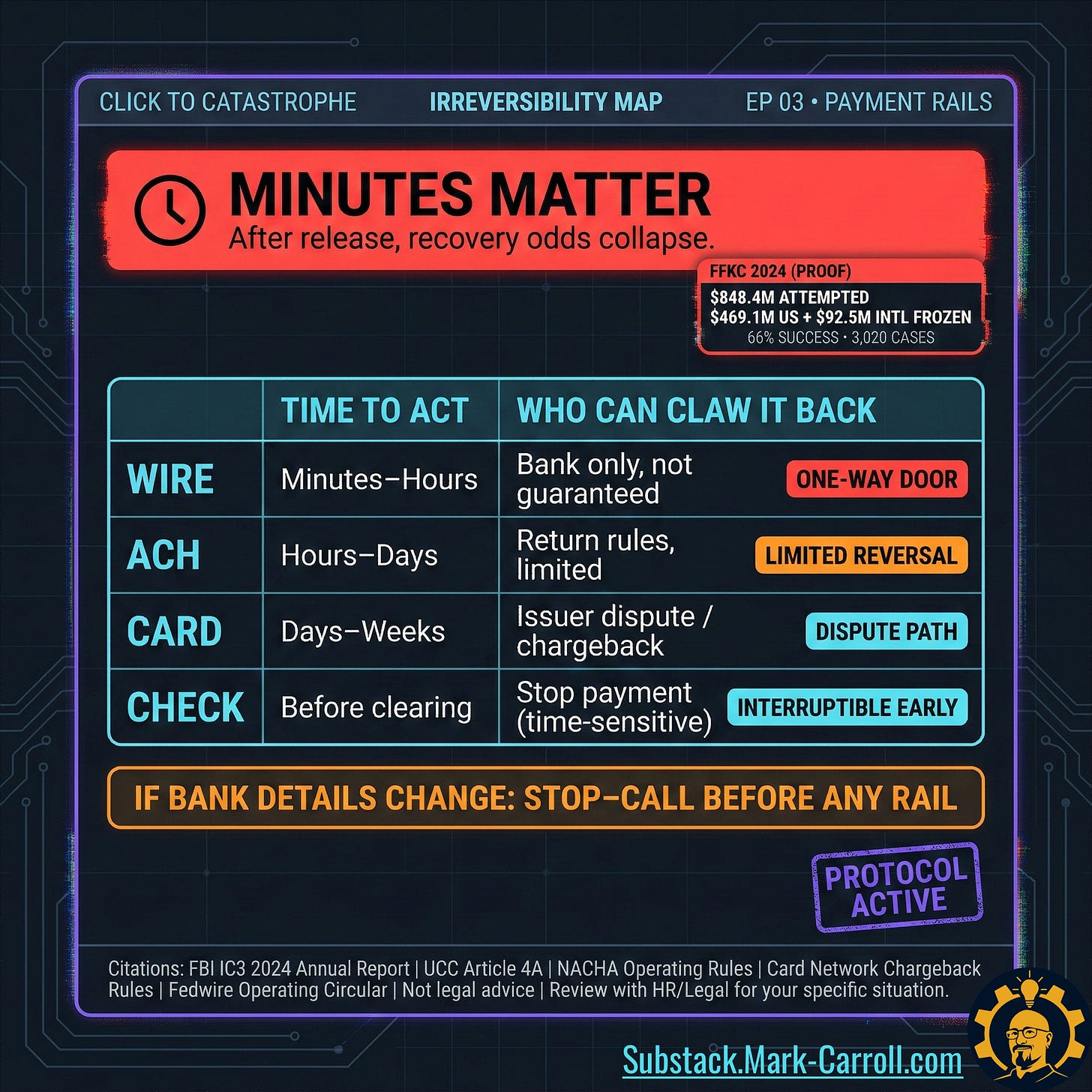
Minutes matter, measured in real money:
IC3 Financial Fraud Kill Chain (FFKC) shows $848.4M in attempted theft in 2024.
IC3 reports $469.1M frozen (domestic) and $92.5M frozen (international).
IC3 reports 3,020 complaints in 2024 with a 66% success rate in freezing funds. (All citations are collected and organized at the bottom of this article in a research binder PDF.)
How to Shut It Down
Winning requires friction at exactly the right step, not “be alert forever” as a lifestyle.
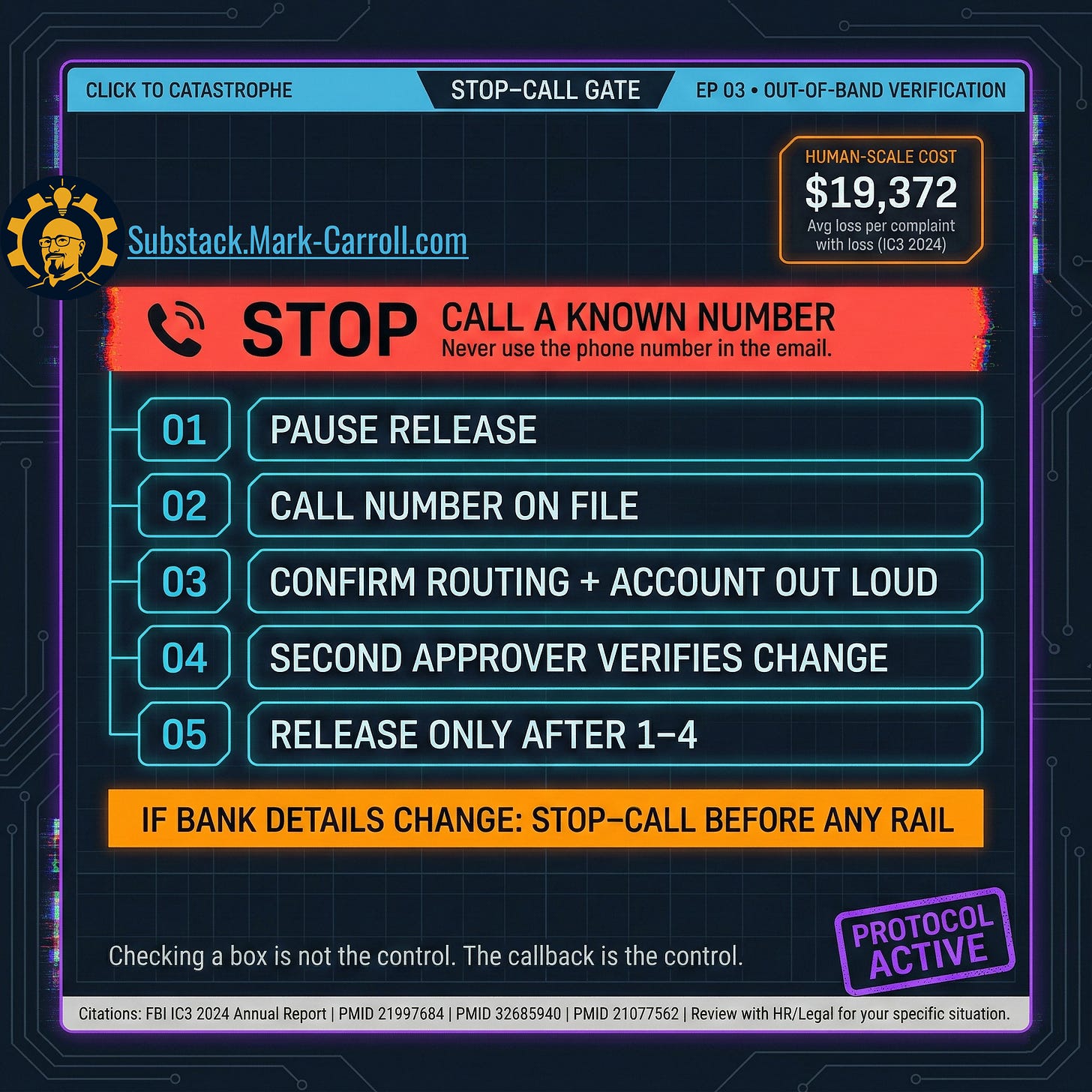
STOP-CALL Gate (Out-of-Band Verification)
The attacker’s win condition is channel control. STOP-CALL is how you leave it.
Rule: if bank details change, stop everything and call a known number before anything else moves.
Known number means the number pulled from your vendor master, contract file, or a previously confirmed call log. Not the email. Not the signature block. Not a number provided in the same message that triggered review.
This call takes less time than the fraud takes to reverse.
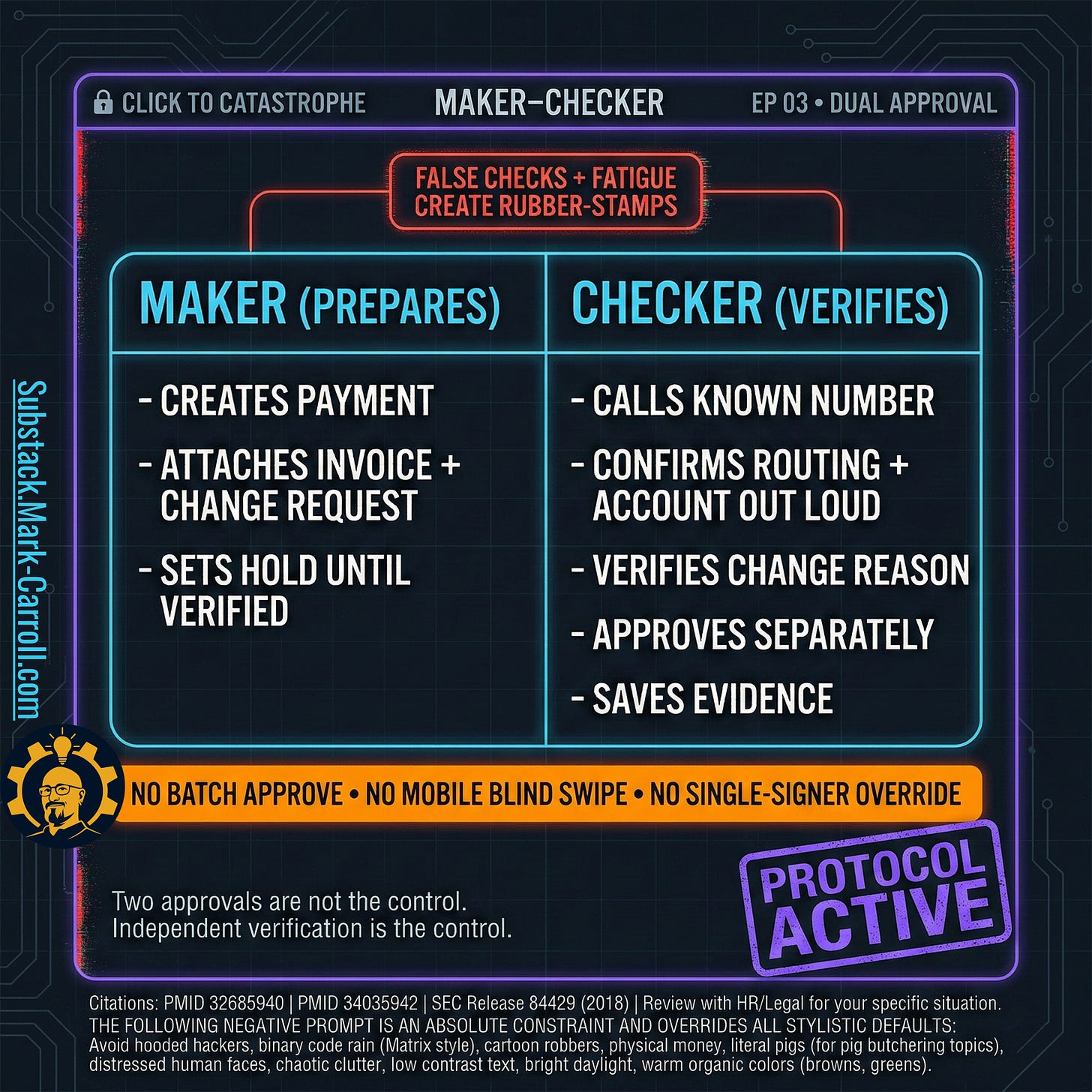
Maker-Checker Dual Approval (Not the Ceremonial Version)
Most organizations already have dual approval on paper. The failure mode is hollow execution.
Ceremonial approval looks like this: two people, both staring at the same email thread and the same vendor record. One approves. The other clicks confirm. Neither spoke to the vendor. Neither verified the bank change through an independent source. Both assumed the other did the hard part.
That produces two signatures on a fraudulent payment.
Maker-checker only works when the second person performs genuinely independent verification, a separate call, a separate source, a separate confirmation, before adding approval. The checker is not a co-signer. The checker is a second investigator.
Hard separation rule: the person who changes vendor bank details cannot be the person who releases funds. No batch approvals. No mobile blind swipes. No single-signer override on a rushed Friday afternoon.