SIM Swap: $26M Risk & 8-Steps to Fix in 1 Hour
🔒 Leader's Dispatch: Volume 31 (Click to Catastrophe, Part 2 of 7 Part Series)
Previous:
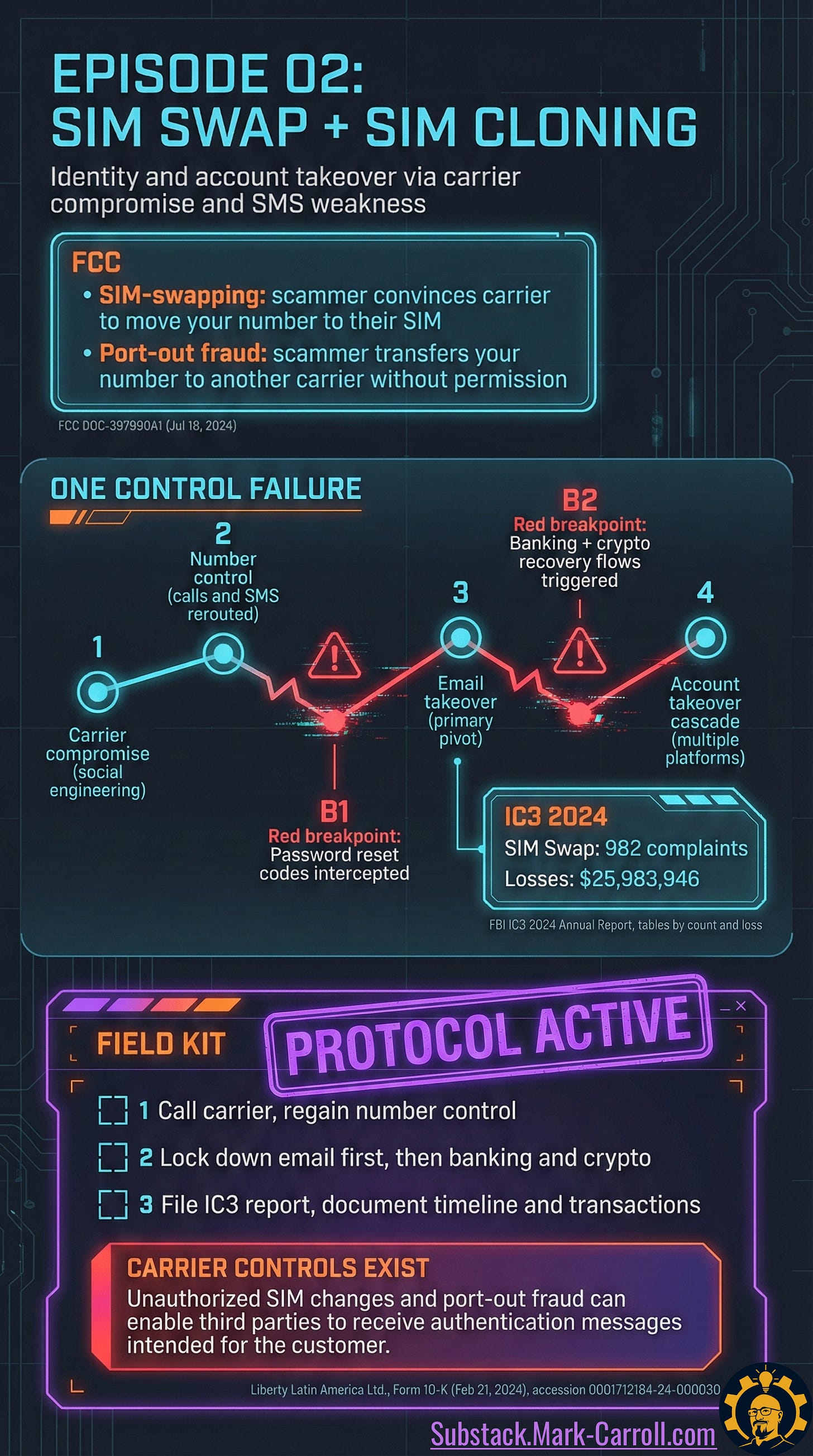
Episode 02: SIM Swap and SIM Cloning
Close the loop…
Your phone goes to No Service in the middle of an ordinary day. Then a carrier email lands that you did not trigger: SIM change completed. That is not a glitch. That is the first audible click of a door you did not open.
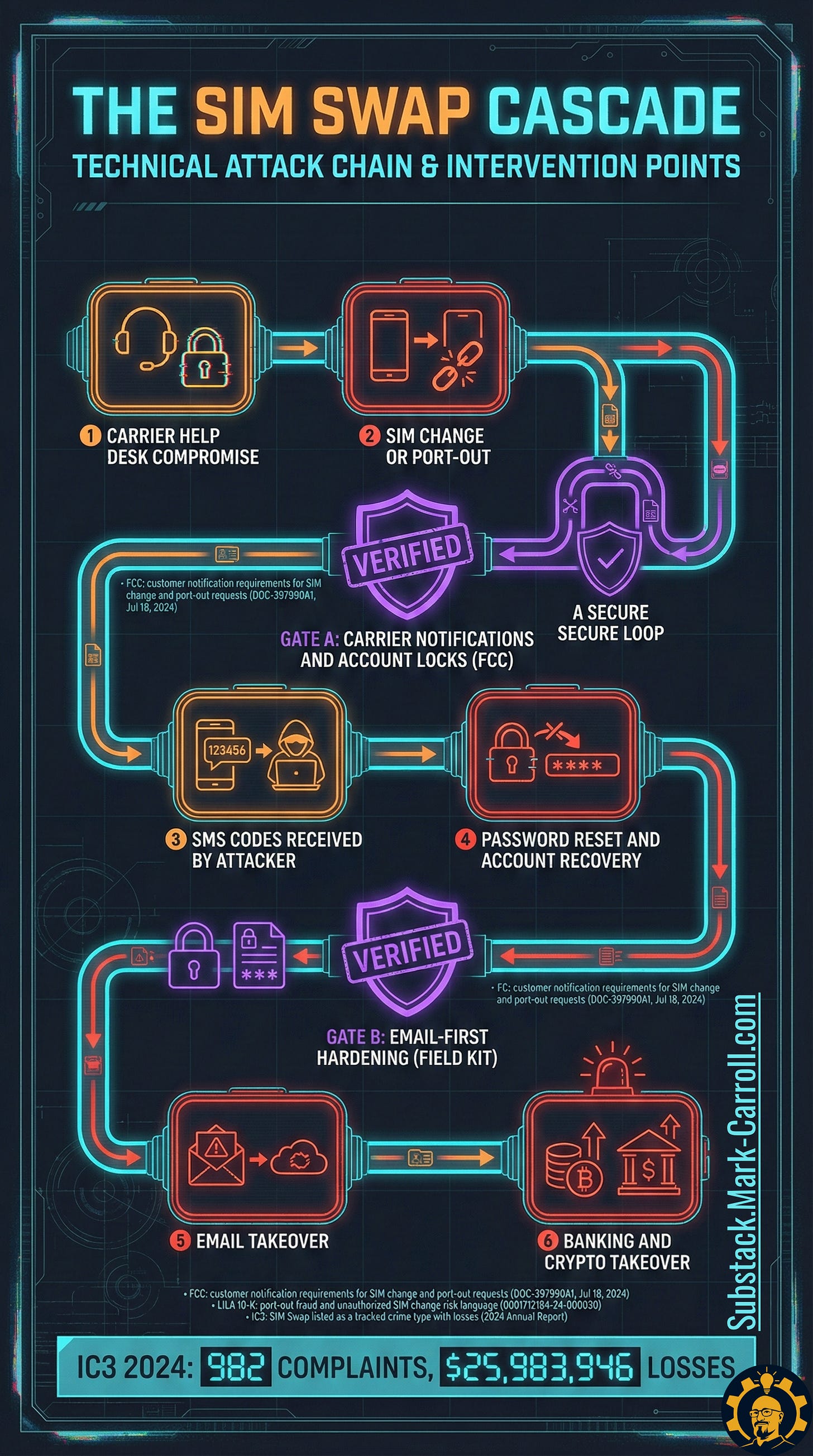
Mechanism: The attacker is not trying to beat your bank. They are trying to control your phone number long enough to receive the one time codes and recovery links that other systems still treat as proof you are you.
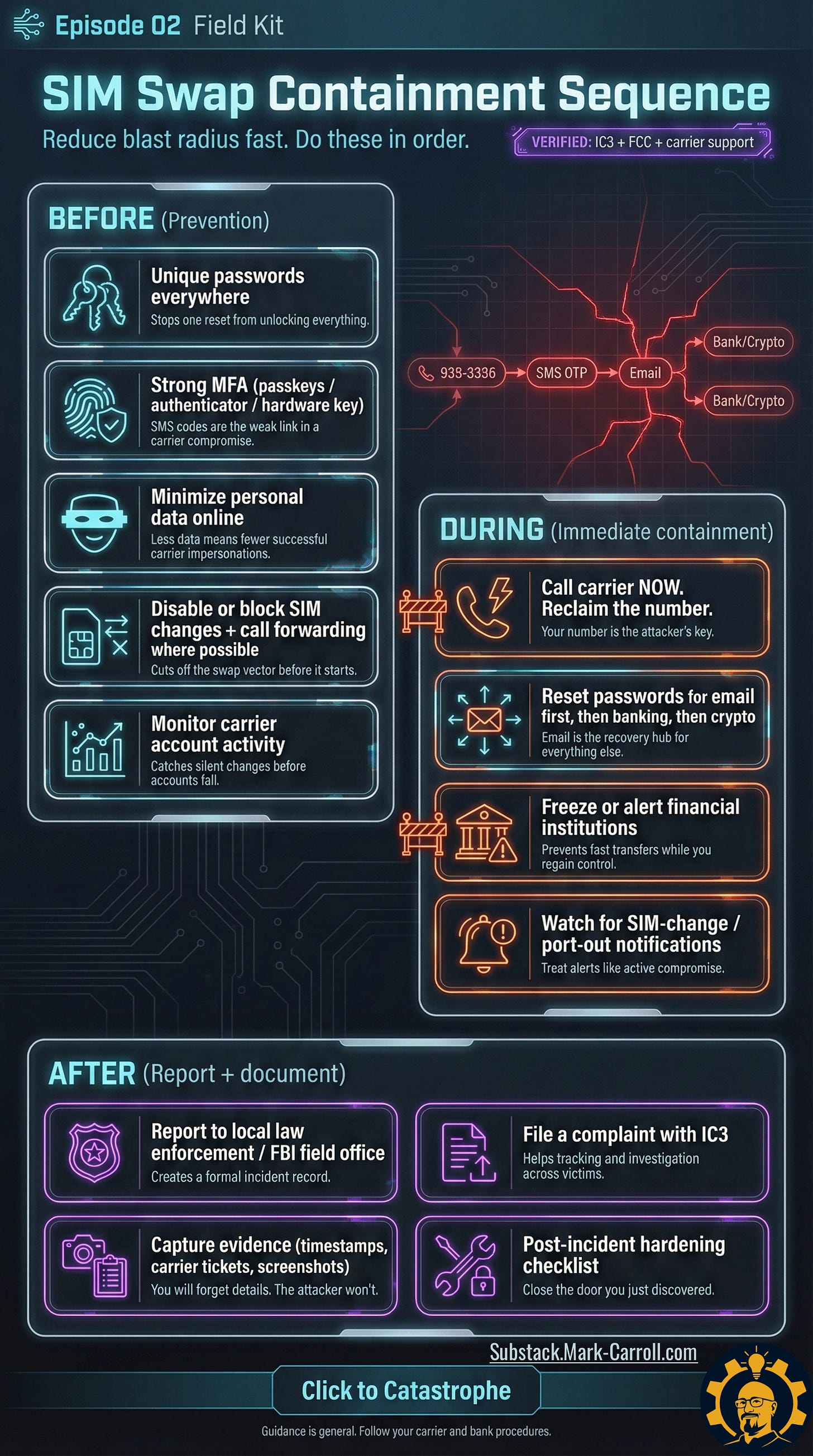
Field kit excerpt: 10 second rule
If No Service + unexpected carrier change alert, assume active compromise. Start the response sequence. Do not troubleshoot signal.
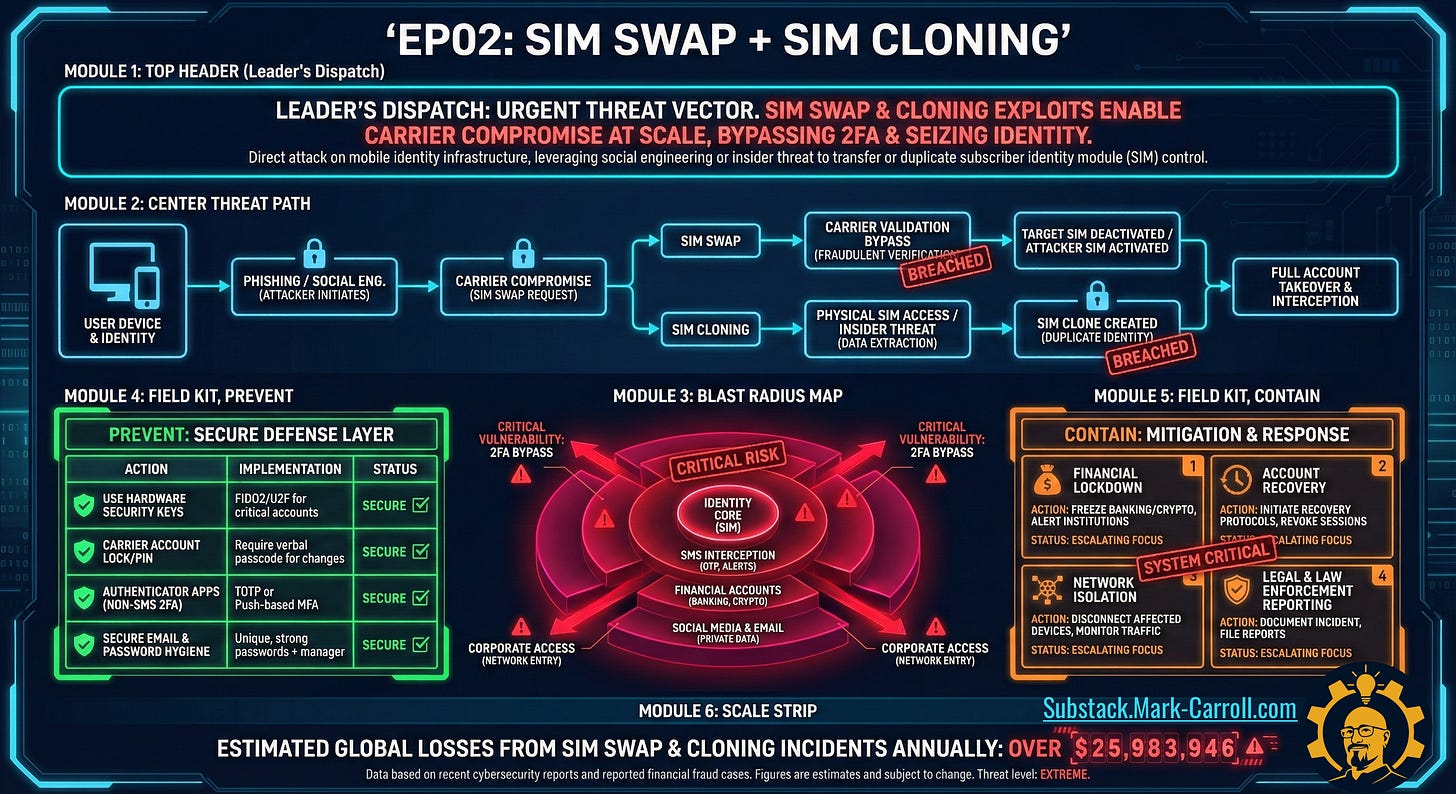
The Five-Step Break-In
How it works
A SIM swap or port out does one thing that matters: it changes who receives your calls and texts. SIM cloning can be a different route, but it aims at the same prize. Control of the identity signal.
Mechanism: Carrier compromise or carrier workflow abuse leads to number control. Number control leads to SMS code interception. SMS code interception leads to password reset and account recovery. Account recovery leads to email takeover, then banking and crypto follow like dominos that think they are being helpful.
Field kit excerpt: The cascade, in one line
Carrier compromise → number control → SMS codes → password reset → email takeover → banking and crypto cascade
How it spreads
This is the part people miss because it feels too normal. Recovery flows are designed to help you, and attackers use that kindness as a highway. Once they own the number, they do not need to “hack” accounts. They request resets and let the systems open the doors for them.
Nightmare consequence scenario (the only one)
You try to secure your bank first because money feels urgent. Meanwhile your email gets reset because the recovery link goes to the attacker. Now every bank alert, every confirmation, every “are you trying to sign in” prompt routes through an inbox you no longer control. You are running in circles while they run in straight lines.
Mechanism: Email is the pivot because it is the recovery hub for everything else. The blast radius is not the phone. The blast radius is everything that trusts the phone.
Field kit excerpt: Two priorities that save hours
Email first.
Anything tied to SMS second.
The Cascade, Translated
Defensive switches
If you want prevention that actually changes outcomes, it is not vibes. It is friction at the carrier. You want two things turned on before you ever need them: immediate alerts, and locks that block changes.
Mechanism: Alerts buy you time. Locks deny the attacker speed. A SIM swap needs a fast, clean handoff. Your job is to make that handoff slow and painful.
Field kit excerpt: Minimum setup in 3 moves
Turn on carrier account lock or SIM protection.
Turn on port out protection or number transfer lock.
Confirm where alerts go (email you control plus a backup number).
Flip These Switches Before Trouble Finds You
Account Locks, Explained Like a Seatbelt
How to shut it down
When this happens, you do not improvise. You run the sequence in order. The goal is not to be perfect. The goal is to contain the blast radius before the cascade spreads.
Mechanism: The attacker needs your number to keep receiving resets. If you reclaim the number fast, you cut off their oxygen. If you secure email next, you stop the downstream resets that keep re infecting everything.