They Never Hacked You, You Invited Them In
🔒 Leader's Dispatch: Volume 34 (Click to Catastrophe, Part 5 of 7 Part Series)
Episode 05: Account Takeover + Fake Support
Research Binder: the receipts (citations + source notes) are compiled in a PDF at the bottom of this article.
Cold Open
You picked up because the call sounded like help.
The trap was not panic alone. The trap was the moment caution got recruited against you.
This episode has one job: make fake-support account takeover recognizable before panic turns cooperation into compromise. By the end, you will know how the pattern works, how it spreads, why false closure happens after the call, and what calmer post-call steps are safer to take next.
Before going further, a plain statement of what this episode is and is not. The strongest evidence behind it supports two things: pre-event recognition and post-event recovery. Research shows that repeated fraud-awareness materials cut re-victimization by more than 22 percent over four months in a randomized trial of older fraud victims. Even a single warning letter cut it by nearly 9 percent. That is the upside story. What the evidence does not support is live-call rescue. A static checklist is not a shield you consult while a scammer is actively steering the conversation. Every directive, every recovery step, and every claim in this episode sits within that boundary. This is not weakness. It is the version most consistent with what the evidence can actually support.
That matters because fake support does not arrive looking like chaos. It arrives looking like relief.

How it works
FRAMEWORK:
Fake support wins by hijacking a decent instinct. Most victims are not being reckless. They are trying to be careful. The attacker does not need you to become careless. The attacker needs you to become cooperative.
Recognition moment 1: the call that sounds like help
First comes contact capture. The attacker gets you onto the most ordinary-feeling route available. A call. A text. A voicemail. A support-looking message. Then comes credibility manufacture. The number looks local. The caller says “fraud department.” They mention suspicious activity. They sound like the fix.

Recognition moment 2: the code handoff
The scam works before the ask. By the time the caller requests a code, asks you to confirm a login, or says they need one more security step, the psychological heavy lifting is already done.
Then the handoff happens. The caller says the code will secure the account. What it may actually do is authorize the attacker’s login, recovery step, or approval prompt. The victim thinks: I am verifying to stop fraud. The attacker uses that same moment to finish the access transfer.
That is why the code is not the lock. It is the key.

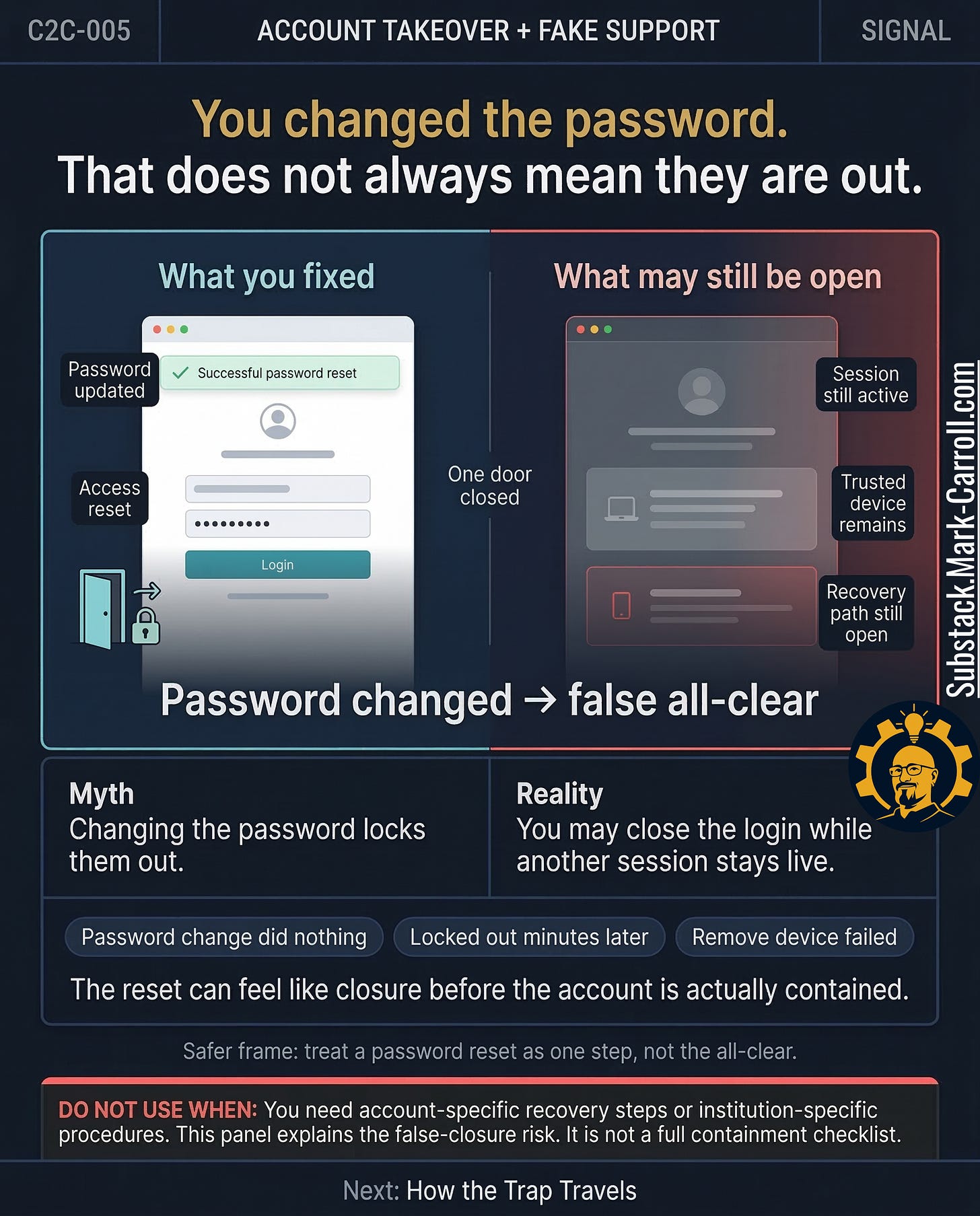
Recognition moment 3: the false all-clear
Then comes the second door. Many victims realize something is wrong, change the password, and feel relief. That reaction makes sense. Unfortunately, “password changed” and “attacker removed” are not always the same event. A live session may still exist. A trusted device may still be remembered. A recovery path may still be open. The reset can feel like closure before the account is actually contained.